Revisiting another YouTube DMCA-themed phishing campaign with old and new pivots
Key Points
- Pivots from the November 2025 investigation produced mixed results: IP and simple hash indicators went inactive quickly, while C2-related response fingerprints that track tooling and configuration continued to surface related infrastructure.
- Malwarebytes’ April 2026 indicators can be amplified in Validin through title-tag and redirect-pattern pivots.
- The newer campaign appears to use a different phishing flow, but both campaigns leave infrastructure-level fingerprints that enable broader discovery.
Background
In November 2025, we looked at a fake “DMCA Takedown” scam targeting YouTube creators. Creators Scott Manley and John Hammond publicly reported the campaign, including a breakdown of the lure, malware, and related infrastructure. The scam attempted to lure victims into downloading malware under the pretense of resolving a copyright complaint.
More recently, in April 2026, Malwarebytes reported a newer fake YouTube copyright notice campaign that used a different flow: a personalized, fake Google login using a Browser-in-the-Browser technique. The sophistication of that toolkit is notable, and we encourage readers to review their write-up.
In this blog post, we explore the following questions:
- Do the search techniques from six months ago yield additional infrastructure?
- Can we use the indicators published by Malwarebytes to uncover more of the campaign?
To answer these questions, we revisited the original pivots and then used the Malwarebytes indicators as starting points for new infrastructure discovery.
Prior Pivots: Dead
Historical DNS
The first pivot, reported by researcher @wbmmfq (Tanner), used Validin’s historical DNS to find domains based on A record history. Within a few days, those domains no longer resolved to that IP address. This immediate transition is apparent in the historical DNS timeline view below.
![Figure 0. Historical DNS view for 101.99.92[.]246 showing the lack of new activity since the original report. Figure 0. Historical DNS view for 101.99.92[.]246 showing the lack of new activity since the original report.](/images/dmca_phishing_revisited/image6.png)
Figure 0. Historical DNS view for 101.99.92[.]246 showing the lack of new activity since the original report.
The story is nearly identical for a second IP address, 101.99.89[.]94, with only the domain 49.amazon-us953[.]com newly resolving since the original report in November.
![Figure 1. Historical DNS view for 101.99.89[.]94 showing only one new resolving domain since the original report. Figure 1. Historical DNS view for 101.99.89[.]94 showing only one new resolving domain since the original report.](/images/dmca_phishing_revisited/image4.png)
Figure 1. Historical DNS view for 101.99.89[.]94 showing only one new resolving domain since the original report.
Across both IP pivots, the observed infrastructure largely stopped reusing the same A-record patterns shortly after the original reporting. Individual IP addresses tend to be among the most ephemeral indicators, so it is not too surprising that these pivots produced little new activity after the original report.
CSS Class
For reference, Validin’s “class hash” pivots fingerprint CSS attributes in the HTML returned by virtual hosts and IP addresses. In November, the HOST-CLASS_0_HASH pivot a927b832d5f0baf0fea5a427588da6c5 led to only a few additional related domains, and the hash had not shown new activity since August. Six months later, that class hash still has not been observed in new activity.
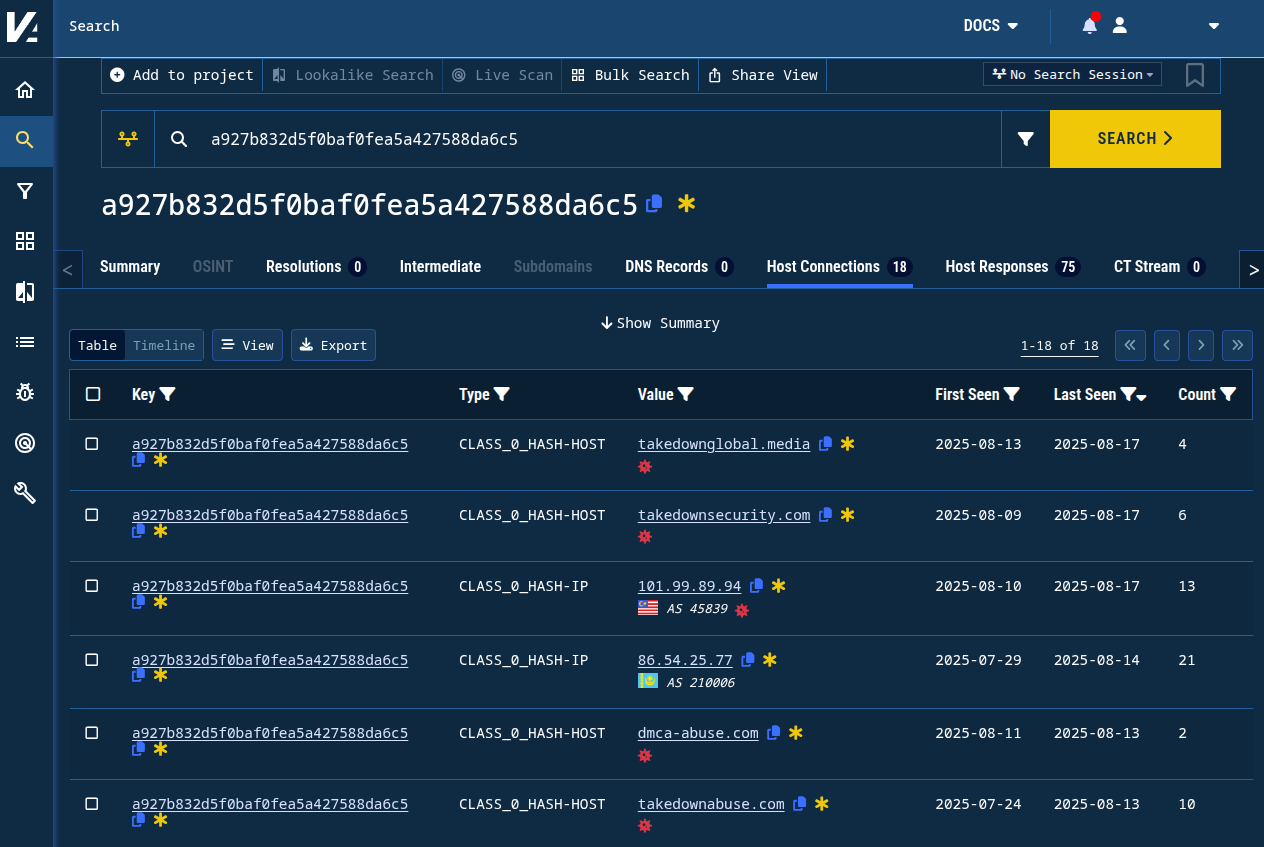
Figure 2. Historic host connections for the hash a927b832d5f0baf0fea5a427588da6c5 still show a most recent “last seen” of August 2025.
Favicon Hash
The favicon hash 1e69c76842689565c2c46580042f2e54 was no longer observed after our blog post and has not been seen since. The second favicon hash noted in the original post, 863a129608d053b67081c8243c72e9e1, was not active at the time of the original post and still has not been observed.
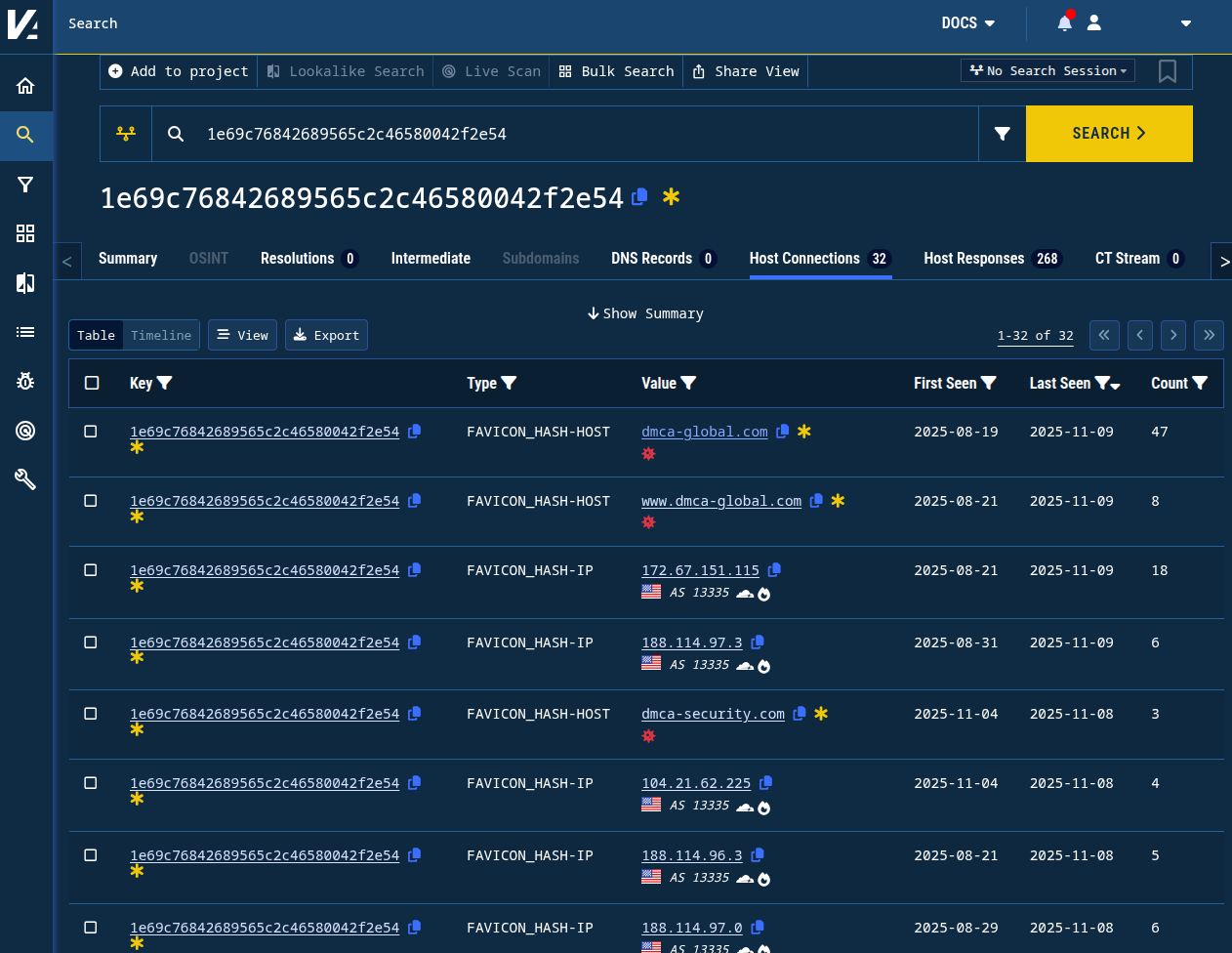
Figure 3. Pivoting on favicon hash shows no new connections to 1e69c76842689565c2c46580042f2e54 since November 2025.
Prior Pivots: Alive
Several pivots from the original blog post continue to surface potentially related infrastructure.
C2 Banner Hash
The banner hash 5dab1fa5f7d42e5eca2385ce3dad1f03 was associated with IP addresses used for C2 in the original malware analysis. Notably, we can see in the two months after our report, five additional IP addresses responded with this distinctive banner hash. Like the others in the original report, these new IP addresses used self-signed certificates with similar naming patterns (e.g. /C=US/ST=New York/L=Seoul/O=SilicoBrain Networks/OU=Helpdesk/CN=recordcustomers.network).
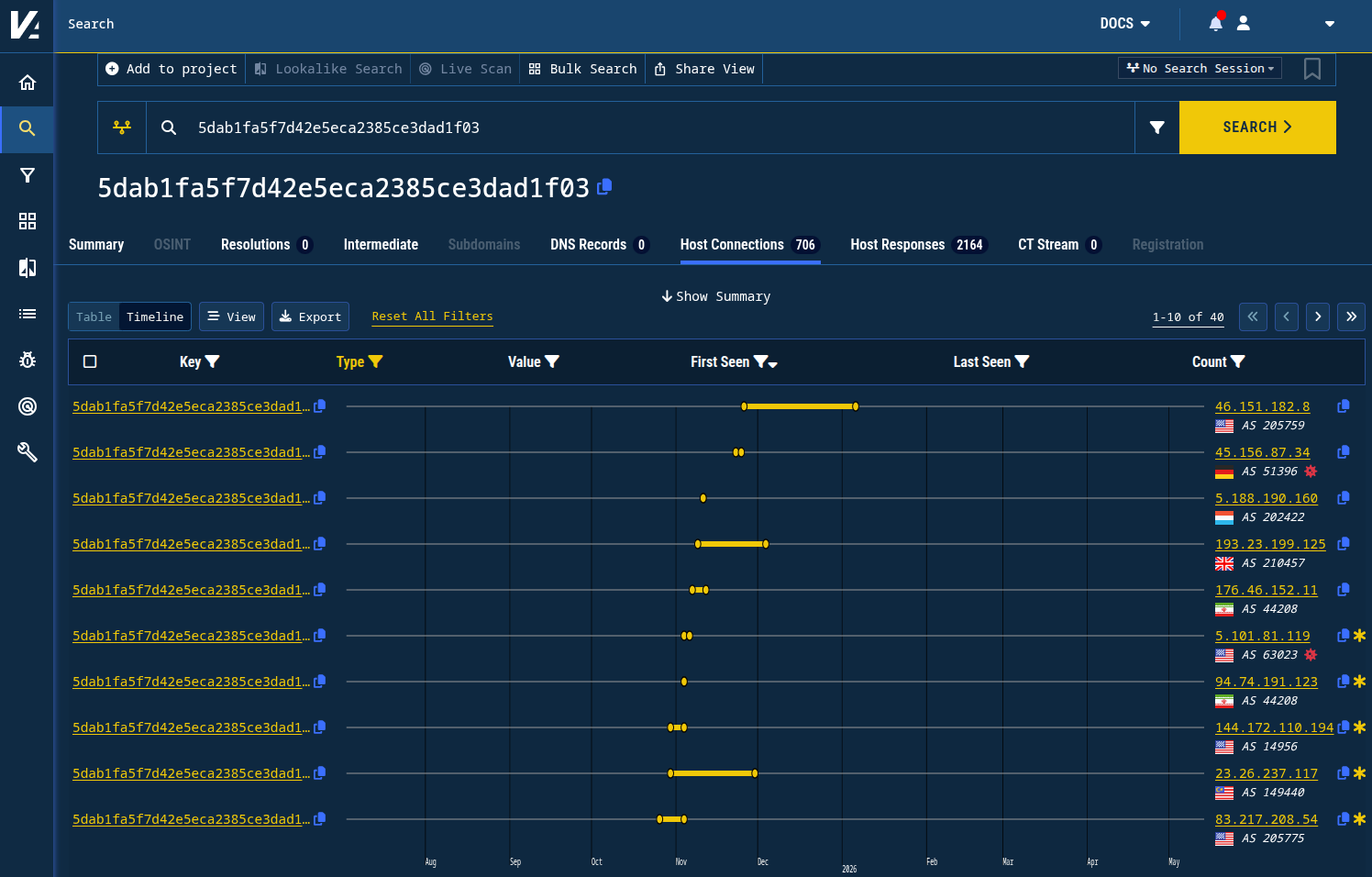
Figure 4. IP addresses associated with the banner hash 5dab1fa5f7d42e5eca2385ce3dad1f03 were observed for months after the original report, as shown in the top five indicators in this table.
46.151.182[.]8
45.156.87[.]34
5.188.190[.]160
193.23.199[.]125
176.46.152[.]11
C2 Header Hash Pivots
Our original report identified several header hashes associated with the C2 domains.
d40097143f9b1abeee08d40097143f9b99e0163dd40097143f9bb3172887
These header hashes captured responses from domains that were all fronted by Cloudflare. In the six months since the last post, most of them have continued to surface new activity.
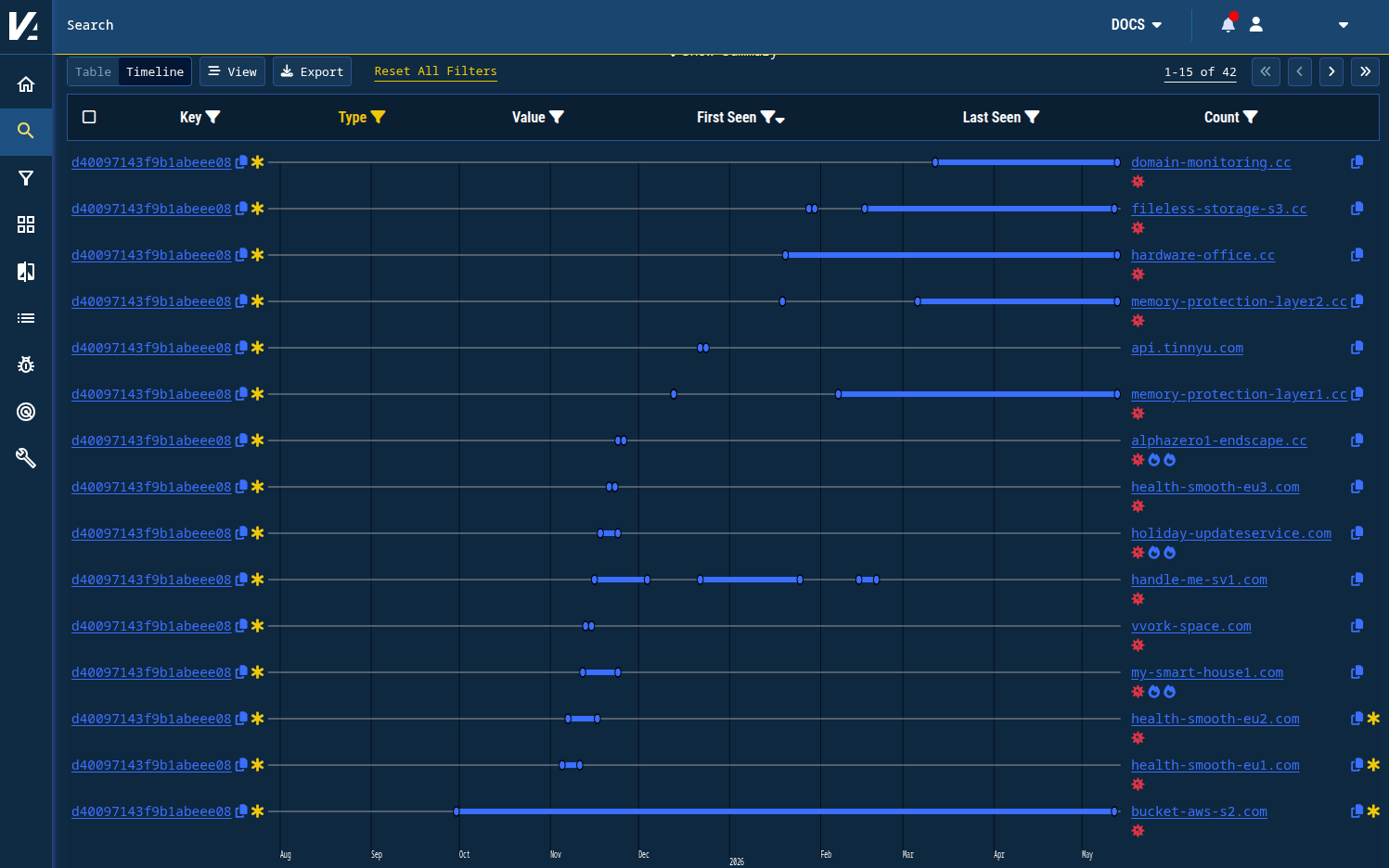
Figure 5. New activity found by tracking host response patterns in a timeline view.
domain-monitoring.cc
fileless-storage-s3[.]cc
hardware-office[.]cc
memory-protection-layer2[.]cc
memory-protection-layer1[.]cc
alphazero1-endscape[.]cc
health-smooth-eu3[.]com
holiday-updateservice[.]com
handle-me-sv1[.]com
vvork-space[.]com
my-smart-house1[.]com
Recent Campaign
The two Malwarebytes indicators we use for the following pivots are:
dmca-notification[.]info(reported as the primary phishing site)blacklivesmattergood4[.]com(reported as a credential-harvesting domain)
We’ll use Validin to pivot on fingerprints left by the threat actor’s domain configuration and identify related infrastructure.
Phishing Lure
Validin crawled the primary phishing site, dmca-notification[.]info, before Cloudflare flagged it for phishing. Using features Validin extracted from that crawl, we can identify a cluster of related domains.
For example, the title-tag value “Yоutubе | Copyright strikes” is associated with hundreds of domain names observed between February 2026 and May 2026. Within the public flags visible in Validin, only the original domain from the Malwarebytes article has been flagged as malicious.
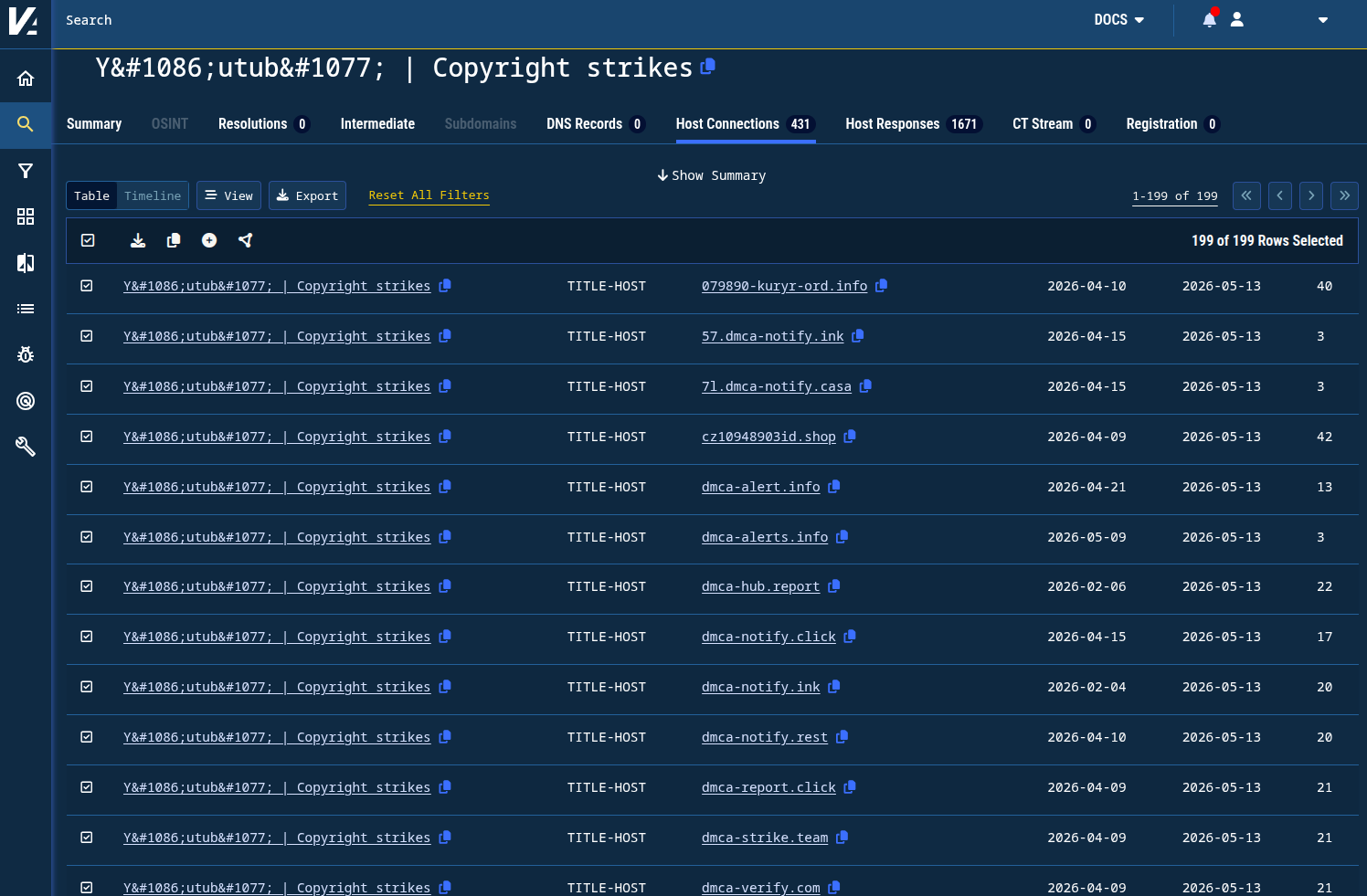
Figure 6. A simple title-tag pivot yields hundreds of related domain names in Validin.
The full list of indicators from this pivot appears at the end of this post.
Credential-Harvesting Domain
The primary phishing lure communicated with blacklivesmattergood4[.]com as a credential-harvesting endpoint. The domain redirects to /youtube/main/ when visited, so we can search for that string and find other domain names that behave the same way.
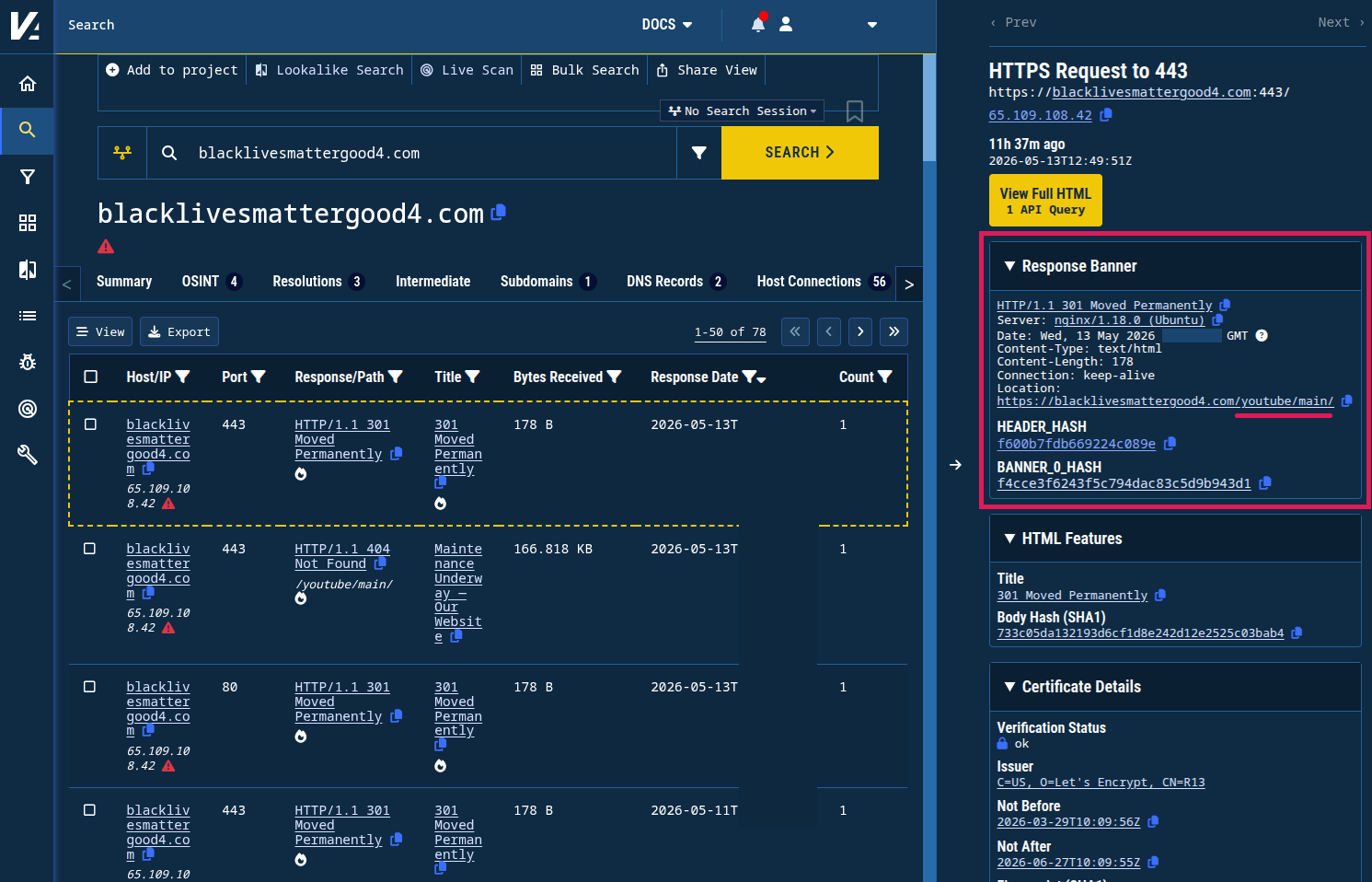
Figure 7. The host response shows a redirect to /youtube/main/ that is fingerprintable in Validin.
Searching Validin for /youtube/main/, we identified nearly 100 other domain names with the same redirect pattern.
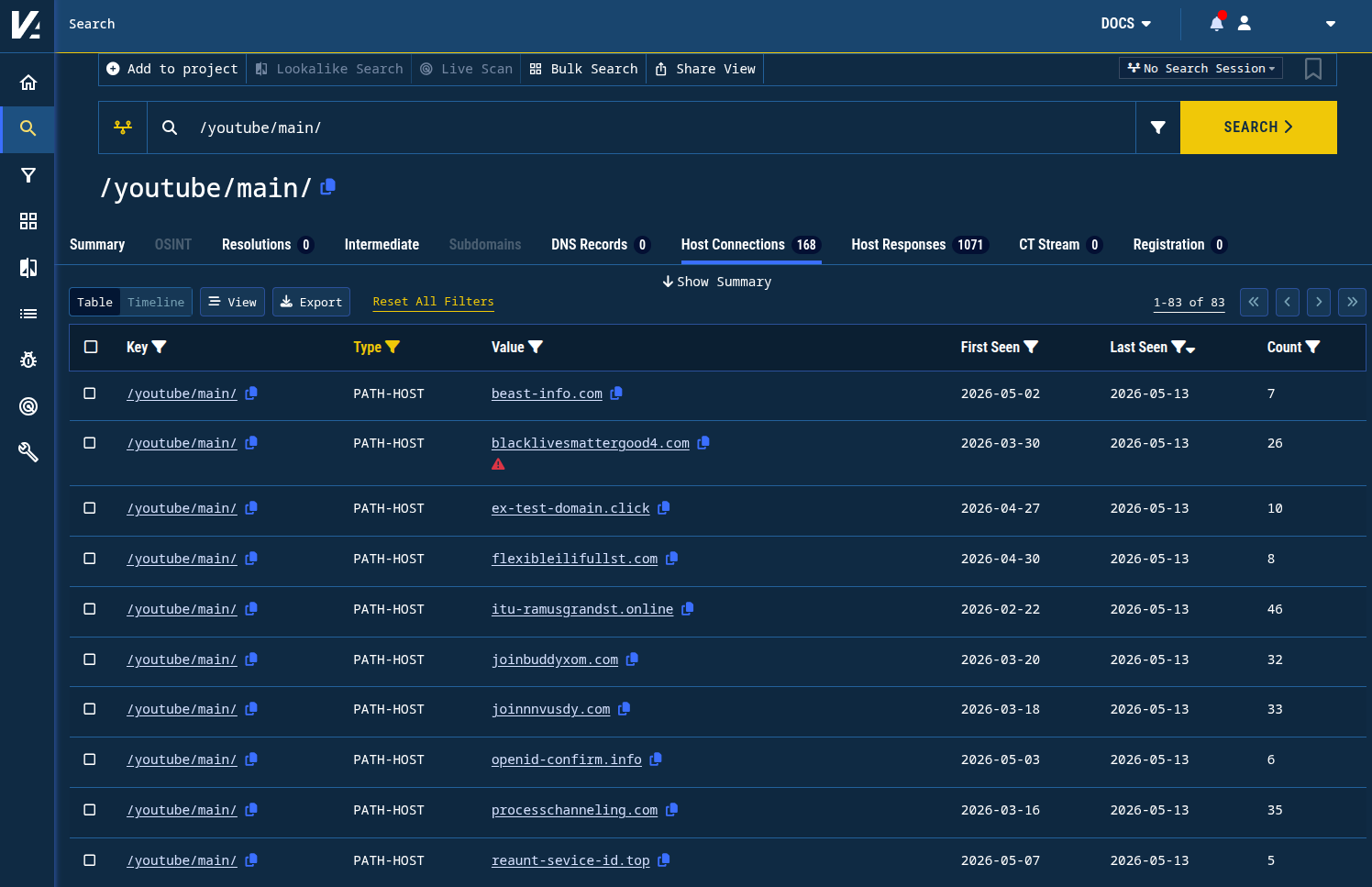
Figure 8. Finding domain names in Validin that share a redirect pattern associated with a credential-harvesting domain name.
The full list of indicators from this pivot appears at the end of this post.
Conclusion
Validin extracts features such as historical DNS, header hashes, title tags, and redirect patterns from domain names and IP addresses, which can be used to identify related infrastructure. While this report is not exhaustive, these examples show how quickly findings can be amplified through Validin’s dataset. This amplification enables broad infrastructure discovery by connecting point-in-time indicators to Validin’s historical and proactive scanning data.
For additional insights into how this credential-harvesting infrastructure works, we captured a live interaction in ANY.RUN that includes indicators from the Malwarebytes report. (Note: We believe many of the captured DNS requests are related to browser-induced preconnection attempts from template randomization, rather than indications of related infrastructure.)
Indicators
dmca-compliance[.]media
video-compliance[.]media
audio-compliance[.]media
content-compliance[.]media
compliance-video[.]media
dmcainfo[.]media
panoramas[.]media
dmca-content[.]media
sweeply[.]media
dmca[.]casa
dmca-strike[.]casa
compliance-video[.]casa
dmca-notify[.]casa
eco-gear[.]club
sweeply[.]cc
media-dmca[.]cfd
youtube-dmca[.]cfd
dmca-media[.]cfd
dmcamedia[.]cfd
dmca-find[.]cfd
dmcafind[.]cfd
dmcatube[.]cfd
dmca-youtube[.]cfd
dmcacheck[.]cfd
dmca-video[.]cfd
dmcavideo[.]cfd
dmca-info[.]cfd
dmcainfo[.]cfd
complaints-report[.]cfd
dmca-gov[.]cfd
sweep-cooperation[.]world
blacklivesmattergood[.]life
mediasync[.]one
mediasync[.]blog
sweeply[.]blog
takedowndmca[.]org
noticetakedown[.]org
takedownalerts[.]org
mediasync[.]sh
support-dmca[.]click
mediasync[.]click
dmca-report[.]click
dmca-support[.]click
dmca-notify[.]click
mediasync[.]ink
dmca-notify[.]ink
collabixagency[.]network
sweeply[.]digital
sweep[.]gl
dmca-strike[.]team
id240941[.]com
dmca-media[.]com
abuse-hub[.]com
dmca-strike[.]com
dmcastrike[.]com
dmcadef[.]com
dmca-check[.]com
strike-check[.]com
dmca-desk[.]com
abuse-desk[.]com
dmca-scan[.]com
dmca-video[.]com
dmcainfo[.]com
dmca-audio[.]com
mobiledownloadapp[.]com
dmcatracker[.]com
strike-monitor[.]com
sync-creators[.]com
takedowncontents[.]com
dmcalerts[.]com
takedownalerts[.]com
dmca-status[.]com
takedownrequest[.]com
dmca-verify[.]com
strike-verify[.]com
report-verify[.]com
dmcaverify[.]com
strikeverify[.]com
dmca[.]forum
sweeply[.]run
mediasync[.]video
sweep[.]video
079890-kuryr-ord[.]info
dmca-notice[.]info
dmca-notification[.]info
takedown-notification[.]info
alert-notification[.]info
mediasync-cooperation[.]info
sweep-cooperation[.]info
dmca-takedown[.]info
dmca-alerts[.]info
dmca-alert[.]info
takedown-alert[.]info
complaints-report[.]info
remove-strike[.]pro
ytstrike[.]pro
strikeremove[.]pro
copyrightviolation[.]pro
pltba09083[.]shop
cz10948903id[.]shop
mediasync[.]top
dmca-notify[.]top
id0144871[.]sbs
id9910875[.]sbs
mediasync-cooperation[.]sbs
compliance-video[.]sbs
complaints-report[.]sbs
dmca-gov[.]sbs
dmca-strike[.]works
sweeply[.]at
notifyhub[.]lat
dmca-notice[.]net
youtube-notice[.]net
dmca-hub[.]report
dmca-strike[.]report
dmca-notify[.]rest
id240941[.]icu
id0976443[.]icu
id0024997[.]icu
id7771029[.]icu
compliance-video[.]icu
dmcaguard[.]cyou
dmcatracker[.]cyou
dmca-notify[.]cyou
mediasync[.]cv
sweeply[.]agency
mediasync[.]my
dmca-notify[.]my
sweeply[.]my
dmca-notify[.]xyz
sweepauth[.]ac
v2auth-f43fui3[.]cc
verify-fu34fuhasfifii99[.]cc
v2oauth-verf33wd[.]cc
verify-fg34fg778ydsvcg[.]cc
toku[.]finance
yt-check-verifi[.]me
auth-identity[.]me
system-identity[.]me
check-verify-id[.]online
check-yt-inform[.]online
auth-secure-connect[.]online
itu-ramusgrandst[.]online
uniswap-labs[.]org
uniswap-awards[.]org
ssl-host[.]org
dns-verify-check[.]click
your-exmaple-domain[.]click
ex-test-domain[.]click
openid-info[.]click
blacklivesmattergood4[.]com
domenadfga[.]com
matreshkabalalaika[.]com
petrushkaskypka[.]com
processingtoyourcab[.]com
ins-guinee[.]com
ins-collecte[.]com
technicallydiff[.]com
technicallystuffoff[.]com
technicallystuff[.]com
processchanneling[.]com
wordsmithcopywriting[.]com
technicalesytexg[.]com
collabix-auth[.]com
swepauth[.]com
ssl-connecti[.]com
sjsisjidkdj[.]com
mavibardak[.]com
docuteamwork[.]com
reasonforcom[.]com
ins-denom[.]com
joinbuddyxom[.]com
basiclogin[.]com
beast-info[.]com
identifime-studio[.]com
verify-studio[.]com
identify-studio[.]com
lodocushgor[.]com
copycompylas[.]com
techsdifferents[.]com
processingtoyourcabinet[.]com
flexibleilifullst[.]com
techdifferentst[.]com
domenayx[.]com
copsforapsslay[.]com
joinnnvusdy[.]com
brandleymedia-verify[.]com
brandleystudio-verify[.]com
system-identify[.]com
studio-identify[.]com
rgph[.]gov[.]gn
openid-confirm[.]info
verify-dns-id[.]to
appverifybrandleylogin2[.]top
asdjifhvliosudhfgv3453[.]top
verify-35iugh777[.]top
sddvwsed-ver88[.]top
reaunt-sevice-id[.]top
verify-brandleypage[.]top
verify-v3u4f3u4hf[.]top
eruigfhisedfrgh-verif[.]top
rtuihgoiujdfhgjbv-verif[.]top
verify-3frewui9of[.]top
au-inform-check[.]top
appverifybrandleylogin[.]top
feknverfno34-verify[.]top
g45oguihsdokj30verify[.]top
dsfoihvgoieurhverify[.]top
brendleygroup[.]app
app-verify-brandleymedia[.]us
lyboy-domains[.]xyz
