Validin is now available as a MISP expansion module, enabling enrichment of MISP events across all Validin data sources
Takeaways
- Validin is now available as a MISP expansion module, enabling enrichment of MISP events across all Validin data sources
- YARA hunts now support both Validin’s virtual host and IPv4 scanning data, expanding visibility to more ports and services.
MISP Integration
The Validin MISP Integration is now available as a MISP expansion module in the misp-modules repository. The module operates similarly to enrichment modules from other internet intelligence providers. The expansion module is available as a single Python file and allows users to enrich MISP events across all of Validin’s data sources.
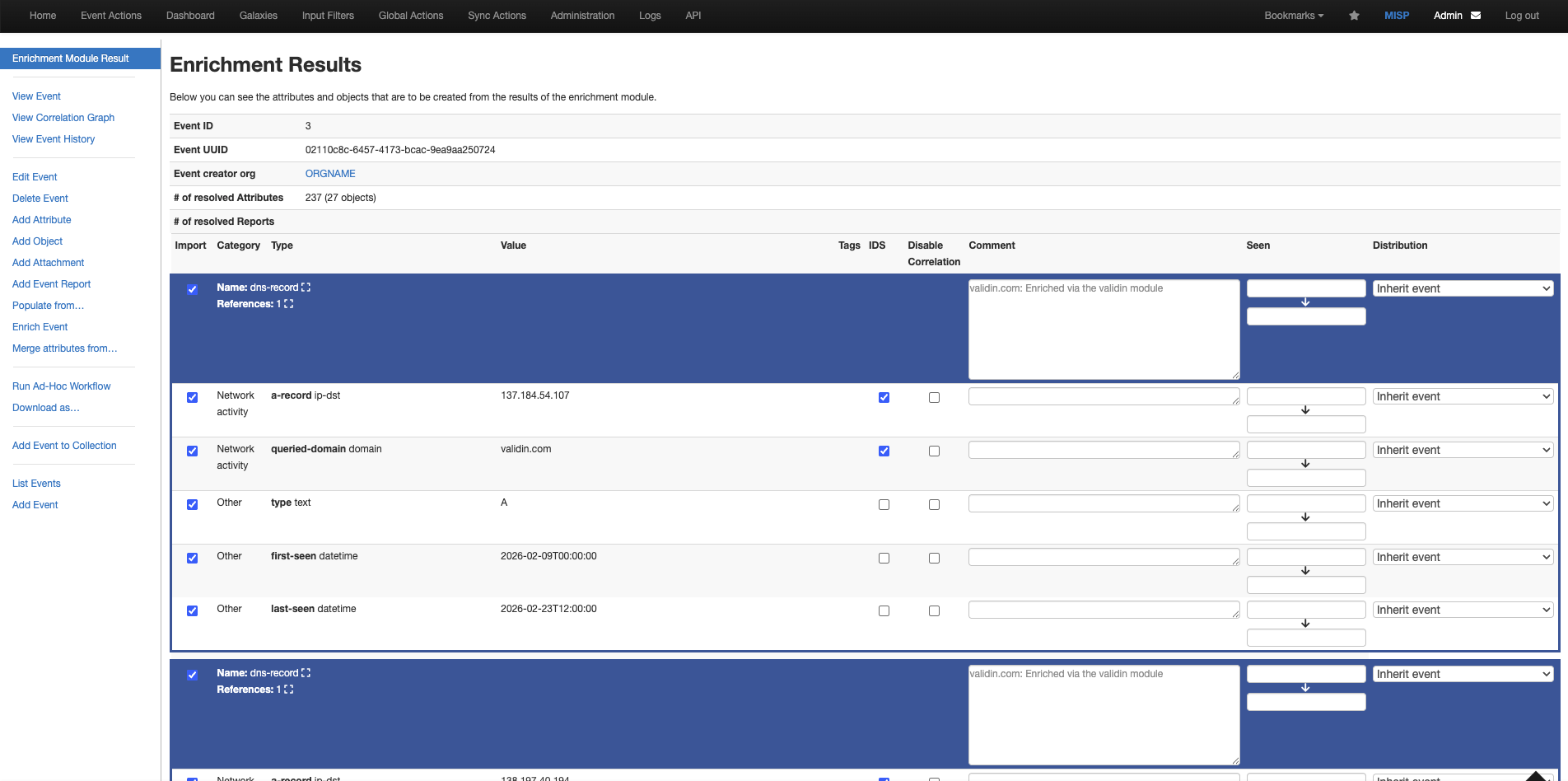
Figure 1. An example of a proposed enrichment for the domain validin.com
The Validin MISP Expansion module enriches the following MISP attribute types:
domainhostnameip-srcip-dst
For every enrichment, Validin enriches across the following data sources:
- DNS (lookback of 14 days)
- Host Responses (lookback of 21 days)
- Registration (lookback of 30 days, for enterprise users only)
- Certificates
- Subdomains
There are two entry points for enrichment:
- Enrichment Mode (Add/Propose enrichment)
- Used to add enriched attributes and records back to the MISP event
- Hover Mode (Show hover enrichment)
- Used to receive immediate context about how a domain/IP is responding
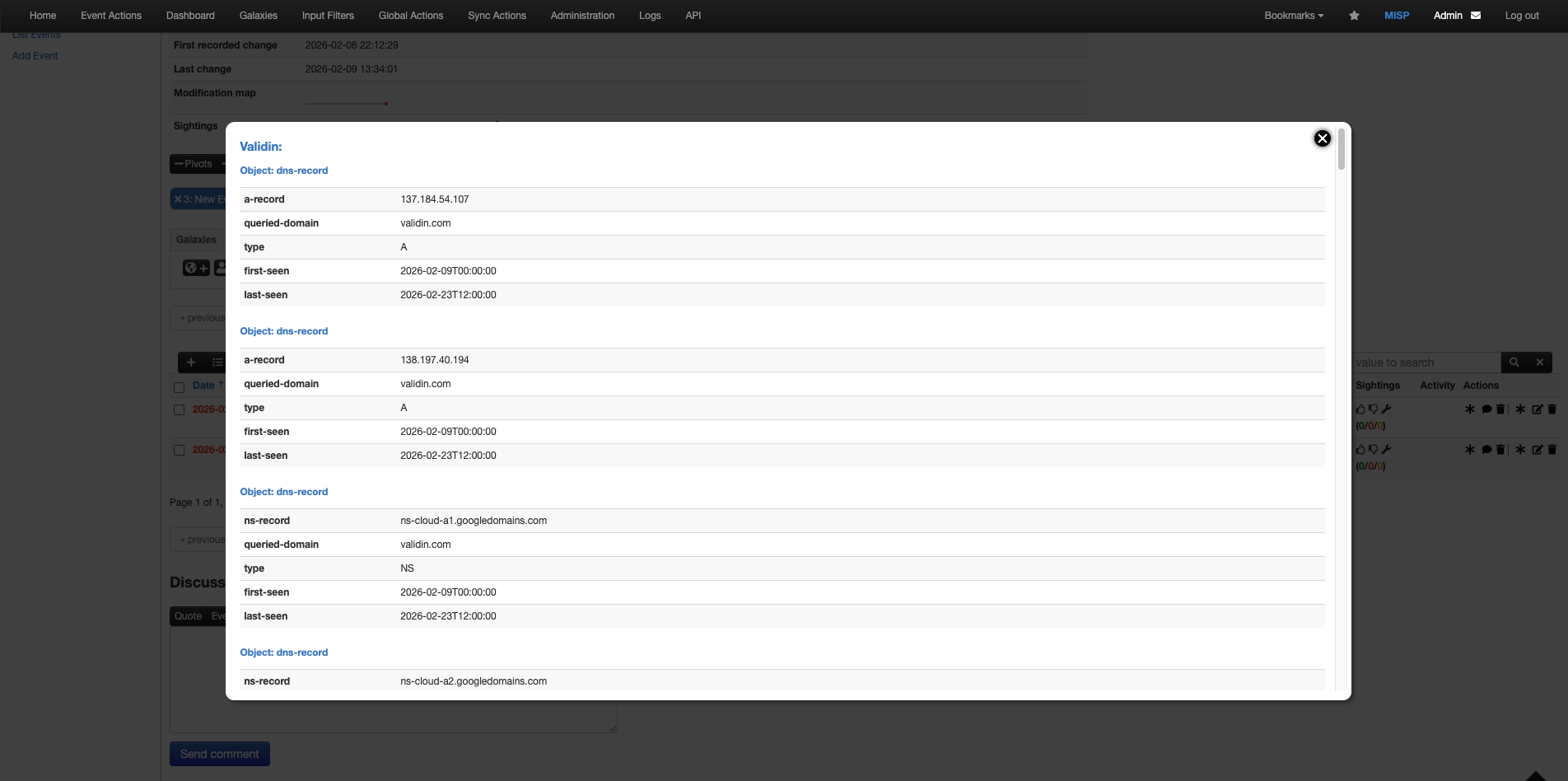
Figure 2. An example of a hover pop-up for validin.com.
Use hover mode to receive immediate context about how infrastructure responds across a variety of data sources.
More details and documentation are available in the Validin Documentation here.
As of February 23rd: Validin’s MISP integration is currently an open PR in the misp-modules repository. Feel free to check it out here, until it is merged by the MISP maintainers.
IPv4 available in YARA
Upon its initial release, our YARA scanning engine only ingested host response data collected from virtual hosts. We have now expanded this to allow hunting across Validin’s active IPv4 scanning as well. When configuring your YARA run, simply check the sources you’d like to scan under the “HTML Response Source” label.
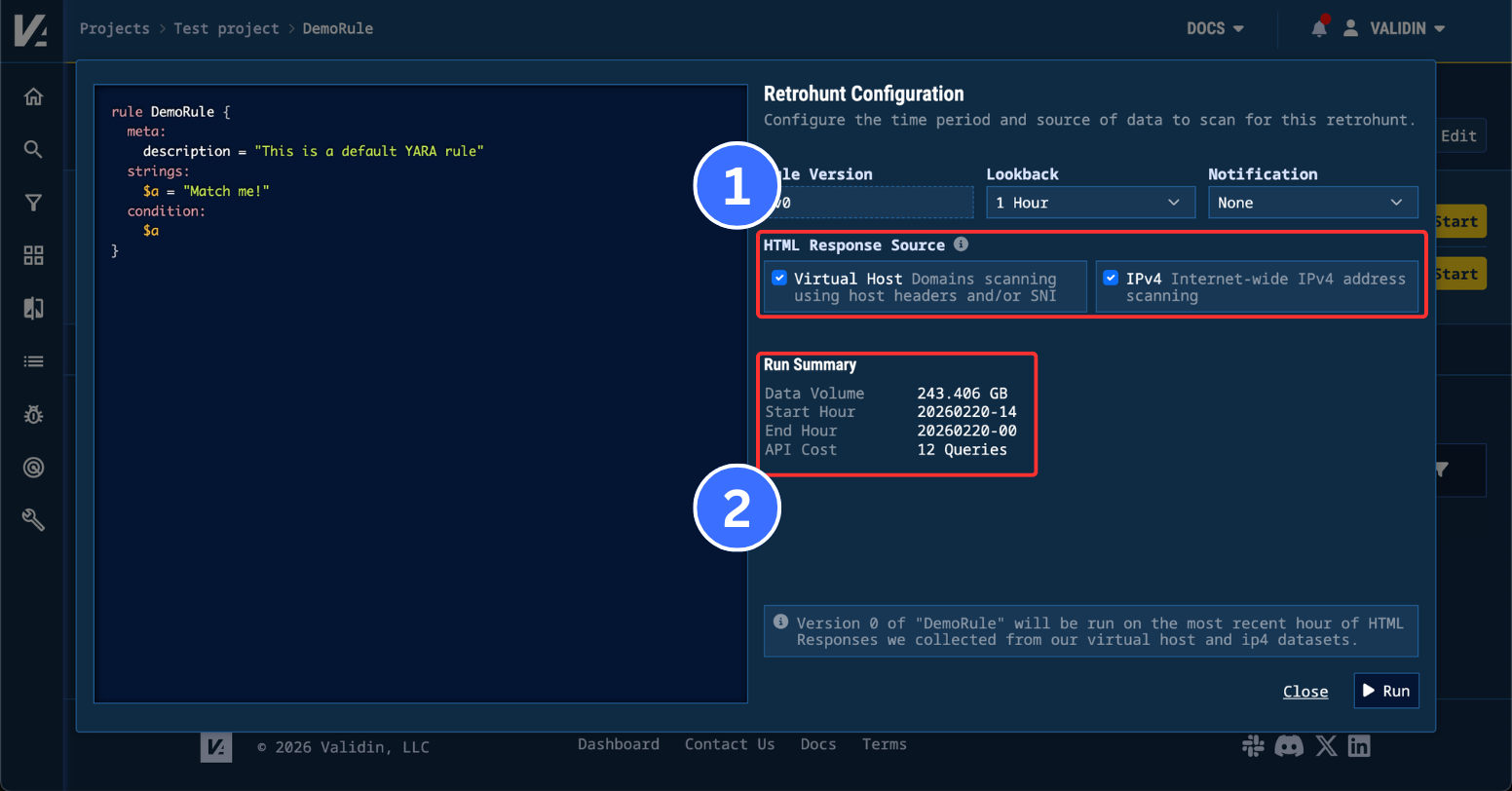
Figure 3. YARA retrohunt configuration in Validin threat intelligence platform
For retro hunts, you’ll see the estimated query usage and data volume update dynamically to reflect the aggregate data available for the selected sources.
One advantage of hunting across Validin’s IPv4 host response data is the port coverage. For our virtual host coverage, only ports 80 and 443 are scanned. However, with our IPv4 scanning, we scan over 50 security-relevant ports, meaning that the typical breadth of discoverable and fingerprintable services with YARA is much larger.
Finding Exposed Telegram Bot Servers with YARA
One of the first use cases the Validin team explored with YARA was tracking exposed API keys. Inspired by SentinelLabs’ LLM-enabled malware analysis, we’ve used the identified patterns, along with additional ones, to track publicly exposed keys over the past several months.
One additional pattern we began tracking was Telegram tokens, suggested by one of our users. Using the regex pattern /[0-9]{8,10}:AA[A-H][a-zA-Z0-9_-]{31,32}/, we can reliably identify embedded tokens used to authenticate Telegram bots for messaging.
When scanning our virtual host data, the rule consistently identified websites using Telegram bots to communicate with their operators. While much of this usage was not overtly malicious, monitoring this rule uncovered some interesting infrastructure.
![Figure 4. Full HTML response for joegotyou[.]cyou Figure 4. Full HTML response for joegotyou[.]cyou](/images/validin-misp-integration-and-yara-improvements/image2.png)
Figure 4. Full HTML response for joegotyou[.]cyou
joegotyou[.]cyou is a great example of this. It appears to be a location-phishing page that sends victims’ coordinates directly to an attacker via a Google Maps link. It stood out because the method of collecting and transmitting location data felt distinct and targeted, but we were unable to identify related campaigns or infrastructure. This was only found through monitoring the YARA Telegram token rule regularly.
However, enabling the IPv4 source for the Telegram token YARA rule uncovered additional exposed infrastructure due to expanded port coverage. We immediately began finding exposed Telegram bot servers on ports 8082 and 8083.
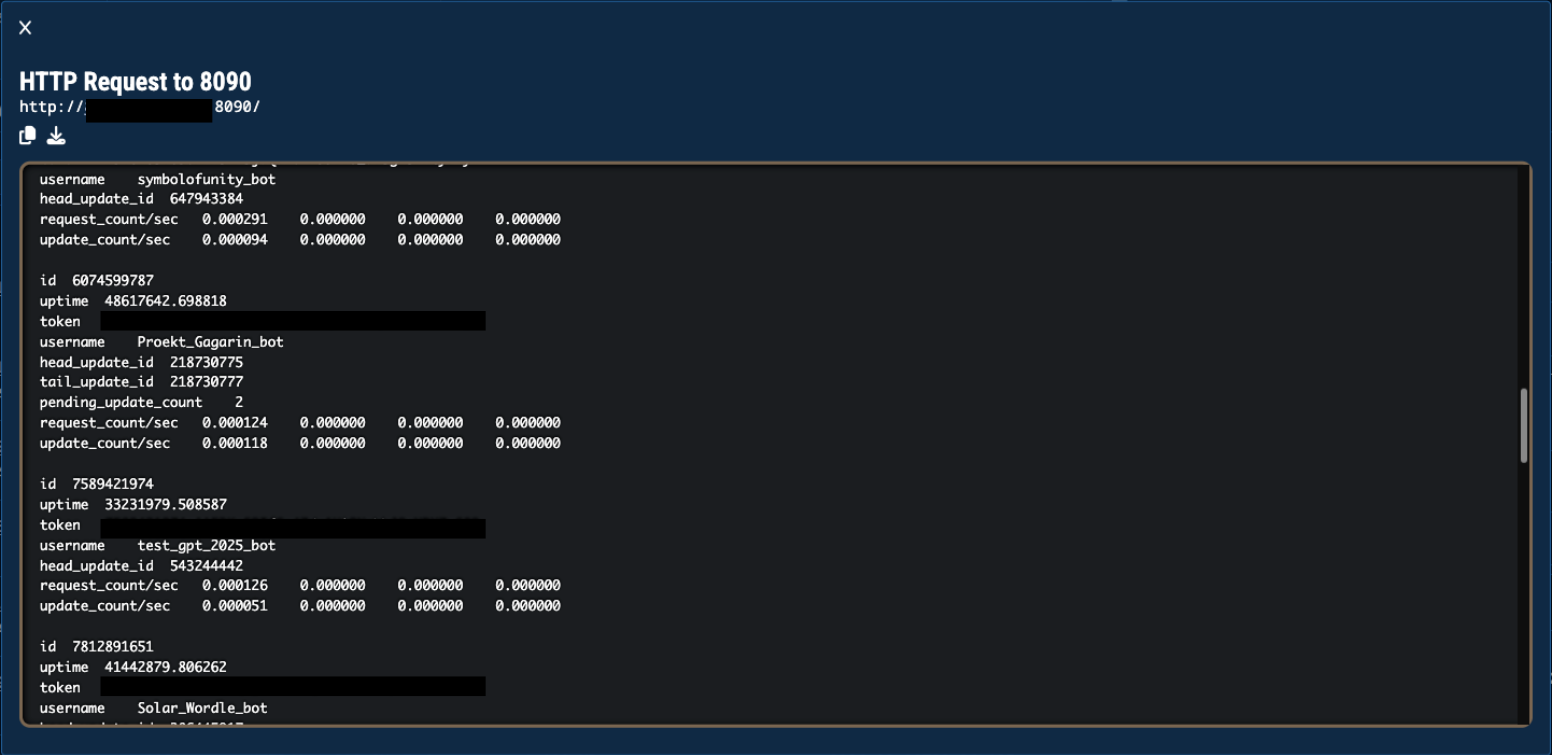
Figure 5. An example of an exposed server found hosting and exposing multiple telegram bots.
Again, an exposed telegram bot token means that you can trivially read the message history of the bot, meaning that exposing entire clusters of your bots’ keys can be quite detrimental. Since this statistics template is distinct and the code for generating the message can be found here, we can create an additional YARA rule that reliably matches this response and continue to monitor the status of this exposed infrastructure.
Conclusion
At Validin, it is our mission to give CTI analysts the best tooling possible to find and operationalize intelligence. Rich integration with CTI tooling is one of the most impactful ways we can do this. If you have specific integrations that would be helpful with you and your workflow please reach out to lets.talk@validin.com.